The US Took Down Record-Breaking Botnets. Then Things Got Worse.
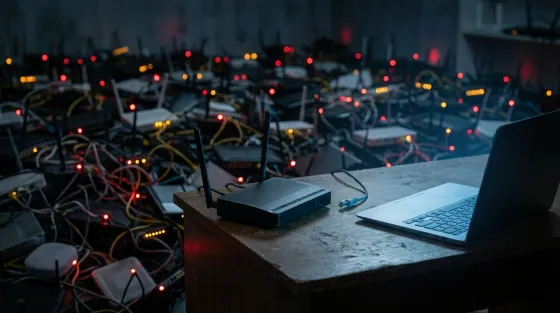
Three Million Zombie Devices and Counting
The US Department of Justice has confirmed the takedown of a cluster of botnets, including Aisuru, Kimwolf, JackSkid, and Mossad, that had collectively infected more than 3 million devices worldwide. Many of those compromised gadgets were sitting inside ordinary home networks, cheerfully participating in record-breaking cyberattacks without their owners having the faintest clue.
This latest action caps off an extraordinary run of botnet busts by US and international law enforcement. But as we have seen repeatedly, dismantling one criminal network often just clears the pitch for the next one.
The Aisuru Problem: Record-Shattering DDoS Power
The Aisuru botnet and its associated variants were responsible for some truly eye-watering DDoS attacks. According to Cloudflare's Q4 2025 threat report, Aisuru set successive records throughout late 2025, culminating in a staggering 31.4 terabits per second attack. That is enough raw bandwidth to make most internet infrastructure buckle at the knees.
With over 3 million infected devices at its disposal, many of them everyday consumer kit like routers, cameras, and smart home gadgets, Aisuru had assembled one of the most powerful DDoS arsenals ever documented. Your broadband router could have been helping to flatten major online services, and you would never have known.
RapperBot: 370,000 Attacks and One Very Googlable Suspect
To understand the Aisuru situation, rewind to August 2025 and the takedown of RapperBot. This DDoS-for-hire service, built on code derived from the notorious Mirai botnet, infected between 65,000 and 95,000 IoT devices and launched over 370,000 attacks against 18,000 victims across 80 countries.
Its largest recorded attack exceeded 6 terabits per second, with typical assaults clocking in at 2 to 3 Tbps. Among its targets: the US Department of Defense Information Network, hit at least three times. RapperBot is also strongly linked to the high-profile X (formerly Twitter) outage on 10 March 2025, the one Elon Musk publicly called a "massive cyberattack." It even reportedly had a go at DeepSeek during China's Spring Festival. Equal opportunity chaos.
The operator turned out to be Ethan Foltz, a 22-year-old from Oregon, charged on 19 August 2025 as part of Operation PowerOFF. Foltz worked with an accomplice known only as "SlayKings," selling attacks for $500 to $10,000 a pop. He faces up to 10 years in prison.
The operational security on display was, to put it charitably, underwhelming. Investigators identified Foltz partly through his PayPal records and over 100 Google searches for "RapperBot" from his own accounts. One hundred searches. From his own accounts. Aspiring cybercriminals, take note.
Here is the critical bit. When RapperBot was dismantled, those tens of thousands of compromised devices did not magically become secure. They sat there, still vulnerable, still running outdated firmware. Aisuru hoovered them up like a bargain hunter at a January sale and grew vastly more powerful. The Aisuru operators reportedly mocked Foltz after his arrest, which tells you everything about the competitive dynamics at play.
SocksEscort: Sixteen Years of Criminal Proxy Service
A separate joint operation between the US and Europol dismantled SocksEscort in February 2026. Less dramatic than the DDoS headline-grabbers, but remarkable for its sheer longevity: this criminal proxy network had been running for approximately 16 years.
SocksEscort infected routers and turned them into proxy nodes, letting criminals route traffic through innocent people's home connections. At takedown, roughly 8,000 routers were infected, with 2,500 in the US alone. Over its lifetime, the network offered access to 369,000 IP addresses across 163 countries.
US authorities seized $3.5 million in cryptocurrency. Europol grabbed 34 domains and 23 servers across 7 countries. Sixteen years of criminal enterprise, parcelled up rather neatly in the end.
The Bigger Picture: Very Expensive Whack-a-Mole
These takedowns represent genuine, coordinated efforts. Major tech firms including Akamai, AWS, Cloudflare, Google, and PayPal assisted the investigations. But the numbers tell an uncomfortable story. DDoS attacks surged 121% in 2025, totalling 47.1 million attacks globally. RapperBot peaked at 6 Tbps; within months of its takedown, Aisuru was hitting 31.4 Tbps.
The fundamental problem remains unsolved. Millions of insecure IoT devices sit on networks worldwide with all the defensive capability of a wet paper bag. When one botnet falls, the vulnerable devices simply get absorbed by the next operator.
What UK Users Should Actually Do
For those of us in the UK, this is not a distant American concern. These botnets operated across 80-plus countries, and proxy networks like SocksEscort spanned 163 nations. The 121% surge in DDoS attacks affects British businesses and infrastructure just as keenly.
The practical advice is both boring and essential: update your router firmware regularly, change default passwords on every connected device, and stop pretending your smart home kit is too obscure to be targeted. It is not. If anything, obscurity makes devices more attractive because manufacturers are less likely to patch them.
The authorities are playing whack-a-mole with increasingly powerful mallets, and that is commendable. But until the underlying problem of millions of insecure connected devices is addressed, every takedown risks being a temporary reshuffling of criminal resources. Foltz faces prison. The next person to exploit those same unpatched devices? Probably already at work.
Read the original article at source.





No comments yet. Be the first to share your thoughts.